(Created target blank page For Version: PSAAS:Public) |
(Modified comment string {{Template:PEC_Migrated| with __NOINDEX__ {{Template:PEC_Migrated|) |
||
| (10 intermediate revisions by 3 users not shown) | |||
| Line 1: | Line 1: | ||
| − | <!-- | + | =Configuring SSO = |
| + | |||
| + | __NOINDEX__ {{Template:PEC_Migrated| | ||
| + | |||
| + | Target=[https://all.docs.genesys.com/PEC-GPA/Current/Administrator/GPlusSSO90 Configuring SSO]}} | ||
| + | |||
| + | |||
| + | |||
| + | You can configure Gplus Adapter to use either your own IDP or Salesforce as an IDP. You can choose one of these two options: | ||
| + | <ol> | ||
| + | <li>'''Gplus Adapter configured with SSO and your own Identity Provider (IDP)'''. | ||
| + | <ul><li>Ensure that SSO for Agent Desktop release 9 has been enabled in your environment by following the instructions in the [[Documentation:PSAAS:Administrator:SAML|Agent Setup SSO article]] and the [[Documentation:PSAAS:Administrator:SingleSignOn|Single Sign-On article]].</li> | ||
| + | <li>To ensure that your IDP does not block access from the <nowiki>genesyscloud.com</nowiki> domain, use the '''Content-Security-Policy''' header setting (refer to [https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Content-Security-Policy/frame-ancestors CSP: frame-ancestors]). | ||
| + | <br/> | ||
| + | For example: '''Content-Security-Policy: frame-ancestors 'self'''' <nowiki>https://*.lightning.force.com;</nowiki> | ||
| + | {{NoteFormat|Do not set '''X-Frame-Options''' to '''SAMEORIGIN'''|3}} | ||
| + | </li> | ||
| + | <li>For SSO logout configuration, use the following Agent Setup Desktop [[Documentation:PSAAS:Administrator:umgrGlobalLogin|Global Login]] options: | ||
| + | <ul> | ||
| + | <li>'''Invalidate Auth SSO session on Workspace logout'''</li> | ||
| + | <li>'''Show Change Account Link'''</li> | ||
| + | </ul> | ||
| + | </li> | ||
| + | <li>Adapter is now ready to use with SSO.</li> | ||
| + | </ul> | ||
| + | <br /><br /></li> | ||
| + | <li>'''Gplus Adapter integrated with [[Documentation:PSAAS:Administrator:GPlusSSO90#SFSSO|Salesforce SSO as the IDP]]'''.<br />This option provides an improved experience over the first option.</li> | ||
| + | </ol> | ||
| + | |||
| + | {{AnchorDiv|SFSSO}} | ||
| + | ==Salesforce as SSO and IDP== | ||
| + | You can simplify your agent log in process by integrating Gplus Adapter with Salesforce to use Salesforce as your single sign-on (SSO) identity provider (IDP). This means that your agent only has to provide their Username and Tenant to log in to Gplus Adapter after they have logged into Salesforce using Salesforce as your SSO identity provider. | ||
| + | |||
| + | Follow these steps to set up SSO with Salesforce as the identity provider: | ||
| + | # [[GPlusSSO90#IDP|Enable Salesforce as an Identity Provider]] | ||
| + | # [[GPlusSSO90#ConnectedApp|Define Gplus Adapter as a Connected App in Salesforce]] | ||
| + | <!-- | ||
| + | {{NoteFormat|SSO is applicable to both test and production environments. Genesys recommends that you test SSO in your testing environment before using it in a production environment.|1}}--> | ||
| + | |||
| + | ===Enable Salesforce as an Identity Provider=== | ||
| + | ====Prerequisites==== | ||
| + | * You must have an Admin role in your organization's Salesforce account | ||
| + | * User email address (username) that you use to login to Salesforce. '''Note:''' Username email addresses must be the same in both Salesforce and Gplus Adapter. | ||
| + | {{AnchorDiv|IDP}} | ||
| + | |||
| + | ====Enable Salesforce as an Identity Provider==== | ||
| + | <ol> | ||
| + | <li>Follow the steps in the [https://help.salesforce.com/articleView?id=identity_provider_enable.htm Enable Salesforce as an Identity Provider] article in the '''Salesforce Help'''.</li> | ||
| + | <li>In the '''Identity Provider''' view, click '''Download Metadata''' to obtain a copy of the IDP metadata XML.</li> | ||
| + | </ol> | ||
| + | {{AnchorDiv|SSOonTenant}} | ||
| + | ===Enable SSO on Genesys tenants=== | ||
| + | <ol> | ||
| + | <li>Employing [https://developers.onelogin.com/saml SAML] for SSO requires two parts, a Service Provider (Genesys Auth Service) and an Identity Provider (Salesforce). To complete your Service Provider configuration, you must upload the Salesforce Identity Provider IDP-metadata XML file you created in the previous procedure to Agent Setup (refer to the [[Documentation:PSAAS:Administrator:SAML|Agent Setup SSO article]]).</li> | ||
| + | <li>Download and open the SP-Metadata XML file in an XML viewer and find the '''Location''' parameter. You will need this parameter for the Entity ID and the ACS URL when you define Gplus Adapter as a Connected App in Salesforce. The '''Location''' URL looks something like this: <tt><nowiki>https://gws-usw1.genhtcc.com/auth/v3/saml/SSO/alias/<string representing the Entity ID></nowiki></tt>.</li> | ||
| + | <li>For SSO logout configuration, use the following Agent Setup Desktop [[Documentation:PSAAS:Administrator:umgrGlobalLogin|Global Login]] options: | ||
| + | <ul> | ||
| + | <li>'''Invalidate Auth SSO session on Workspace logout'''</li> | ||
| + | <li>'''Show Change Account Link'''</li> | ||
| + | </ul> | ||
| + | </li> | ||
| + | </ol> | ||
| + | {{AnchorDiv|ConnectedApp}} | ||
| + | |||
| + | ===Define Gplus Adapter as a Connected App in Salesforce=== | ||
| + | <ol> | ||
| + | <li>To configure a new Connected App follow the instructions in the Salesforce Help [https://help.salesforce.com/articleView?id=service_provider_define.htm&type=5 Defining Service Providers as SAML-Enabled Connected Apps] document.</li> | ||
| + | <li>Specify the required fields under '''Basic Information''': | ||
| + | <ul> | ||
| + | <li>Connected App Name (for example, Gplus Adapter)</li> | ||
| + | <li>API Name (for example, GWS)</li> | ||
| + | <li>Contact email (the email address of the Admin user)</li> | ||
| + | </ul> | ||
| + | </li> | ||
| + | <li>Under Web App Settings, select '''Enable SAML'''</li> | ||
| + | <li>Use the '''Location''' string from the SP-Metadata xml file of the Enable Salesforce as an Identity Provider procedure to provide Entity ID and ACS URL: | ||
| + | <ul> | ||
| + | <li>Entity ID: The long string of numbers and letters at the end of the '''Location''' parameter URL after the last "/". </li> | ||
| + | <li>ACS URL: The URL from the '''Location''' parameter that you obtained from the SP-Metadata in step 2 of the ''Enable SSO on Genesys tenants'' procedure.</li> | ||
| + | </ul> | ||
| + | [[File:Gplus_900_Salesforce_Setup_New_Connected_App_View.png|500px]] | ||
| + | </li> | ||
| + | <li>Use the [https://help.salesforce.com/articleView?id=identity_provider_error_log.htm&type=5 identity provider event log] to troubleshoot errors when trying to log in to Gplus Adapter.</li> | ||
| + | </ol> | ||
| + | |||
| + | ===Agent SSO login workflow=== | ||
| + | This is the general workflow when Gplus Adapter initiates the login process and uses Salesforce to identify the user: | ||
| + | # An agent logs in to Salesforce. | ||
| + | # The agent provides their Username and Tenant name in Gplus Adapter and clicks '''Next'''. | ||
| + | # GPlus Adapter sends a request to Salesforce to authenticate the user. | ||
| + | # Salesforce identifies the agent specified in the request and sends an authentication response. | ||
| + | # Gplus Adapter authenticates the response sent by Salesforce. | ||
| + | # If the agent is authenticated, they are logged in to Gplus Adapter while logged in to Salesforce. | ||
| + | |||
| + | ====Useful links==== | ||
| + | * [https://developer.salesforce.com/docs/atlas.en-us.externalidentityImplGuide.meta/externalidentityImplGuide/external_identity_provide_sso.htm Salesforce guide] | ||
| + | * [http://salesforce.vidyard.com/watch/I6j0O6jqr8ZTtoj5Wm_Fjg Video example from Salesforce] | ||
| + | <!--* [https://help.mypurecloud.com/articles/about-single-sign-on-sso/ Example of the same SSO implementation in Genesys Cloud]--> | ||
| + | |||
| + | [[Category:V:PSAAS:Public]] | ||
Latest revision as of 08:56, November 9, 2020
Configuring SSO
Important
This content may not be the latest Genesys Engage cloud content. To find the latest content, go to Configuring SSO.
You can configure Gplus Adapter to use either your own IDP or Salesforce as an IDP. You can choose one of these two options:
- Gplus Adapter configured with SSO and your own Identity Provider (IDP).
- Ensure that SSO for Agent Desktop release 9 has been enabled in your environment by following the instructions in the Agent Setup SSO article and the Single Sign-On article.
- To ensure that your IDP does not block access from the genesyscloud.com domain, use the Content-Security-Policy header setting (refer to CSP: frame-ancestors).
For example: Content-Security-Policy: frame-ancestors 'self' https://*.lightning.force.com;WarningDo not set X-Frame-Options to SAMEORIGIN - For SSO logout configuration, use the following Agent Setup Desktop Global Login options:
- Invalidate Auth SSO session on Workspace logout
- Show Change Account Link
- Adapter is now ready to use with SSO.
- Gplus Adapter integrated with Salesforce SSO as the IDP.
This option provides an improved experience over the first option.
Salesforce as SSO and IDP
You can simplify your agent log in process by integrating Gplus Adapter with Salesforce to use Salesforce as your single sign-on (SSO) identity provider (IDP). This means that your agent only has to provide their Username and Tenant to log in to Gplus Adapter after they have logged into Salesforce using Salesforce as your SSO identity provider.
Follow these steps to set up SSO with Salesforce as the identity provider:
Enable Salesforce as an Identity Provider
Prerequisites
- You must have an Admin role in your organization's Salesforce account
- User email address (username) that you use to login to Salesforce. Note: Username email addresses must be the same in both Salesforce and Gplus Adapter.
Enable Salesforce as an Identity Provider
- Follow the steps in the Enable Salesforce as an Identity Provider article in the Salesforce Help.
- In the Identity Provider view, click Download Metadata to obtain a copy of the IDP metadata XML.
Enable SSO on Genesys tenants
- Employing SAML for SSO requires two parts, a Service Provider (Genesys Auth Service) and an Identity Provider (Salesforce). To complete your Service Provider configuration, you must upload the Salesforce Identity Provider IDP-metadata XML file you created in the previous procedure to Agent Setup (refer to the Agent Setup SSO article).
- Download and open the SP-Metadata XML file in an XML viewer and find the Location parameter. You will need this parameter for the Entity ID and the ACS URL when you define Gplus Adapter as a Connected App in Salesforce. The Location URL looks something like this: https://gws-usw1.genhtcc.com/auth/v3/saml/SSO/alias/<string representing the Entity ID>.
- For SSO logout configuration, use the following Agent Setup Desktop Global Login options:
- Invalidate Auth SSO session on Workspace logout
- Show Change Account Link
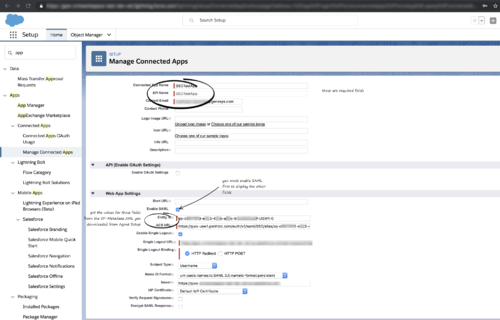
Define Gplus Adapter as a Connected App in Salesforce
- To configure a new Connected App follow the instructions in the Salesforce Help Defining Service Providers as SAML-Enabled Connected Apps document.
- Specify the required fields under Basic Information:
- Connected App Name (for example, Gplus Adapter)
- API Name (for example, GWS)
- Contact email (the email address of the Admin user)
- Under Web App Settings, select Enable SAML
- Use the Location string from the SP-Metadata xml file of the Enable Salesforce as an Identity Provider procedure to provide Entity ID and ACS URL:
- Entity ID: The long string of numbers and letters at the end of the Location parameter URL after the last "/".
- ACS URL: The URL from the Location parameter that you obtained from the SP-Metadata in step 2 of the Enable SSO on Genesys tenants procedure.
- Use the identity provider event log to troubleshoot errors when trying to log in to Gplus Adapter.
Agent SSO login workflow
This is the general workflow when Gplus Adapter initiates the login process and uses Salesforce to identify the user:
- An agent logs in to Salesforce.
- The agent provides their Username and Tenant name in Gplus Adapter and clicks Next.
- GPlus Adapter sends a request to Salesforce to authenticate the user.
- Salesforce identifies the agent specified in the request and sends an authentication response.
- Gplus Adapter authenticates the response sent by Salesforce.
- If the agent is authenticated, they are logged in to Gplus Adapter while logged in to Salesforce.
Useful links
This page was last edited on November 9, 2020, at 08:56.
Comments or questions about this documentation? Contact us for support!